Blog
The Hidden Cost of Forced Upgrades: Rethinking the Economics of Software Security
In a landscape defined by complex software supply chains, the most effective strategy may not be constant movement forward. It may be something simpler.

John Amaral
CTO, Co-Founder
Published :
Mar 3, 2026
For much of the history of software, upgrading was synonymous with improving security. New versions delivered patches, closed vulnerabilities, improved cryptographic implementations, and often introduced valuable new capabilities. If a flaw was discovered, the answer was simple: upgrade to the version where it had been fixed.
In an earlier era of software, that approach worked well. Applications were smaller, dependency chains were shorter, and version upgrades tended to be relatively contained events. Moving forward to a new version meant receiving a handful of improvements and fixes.
Modern software systems operate under very different conditions. Today’s applications are constructed from vast layers of dependencies: operating system packages, language runtimes, frameworks, direct libraries, and large webs of transitive dependencies. A single service can incorporate hundreds or even thousands of upstream components. In this environment, version upgrades are rarely isolated changes. They are often sweeping movements across dependency trees.
What was once a straightforward security mechanism has quietly evolved into a source of operational instability.
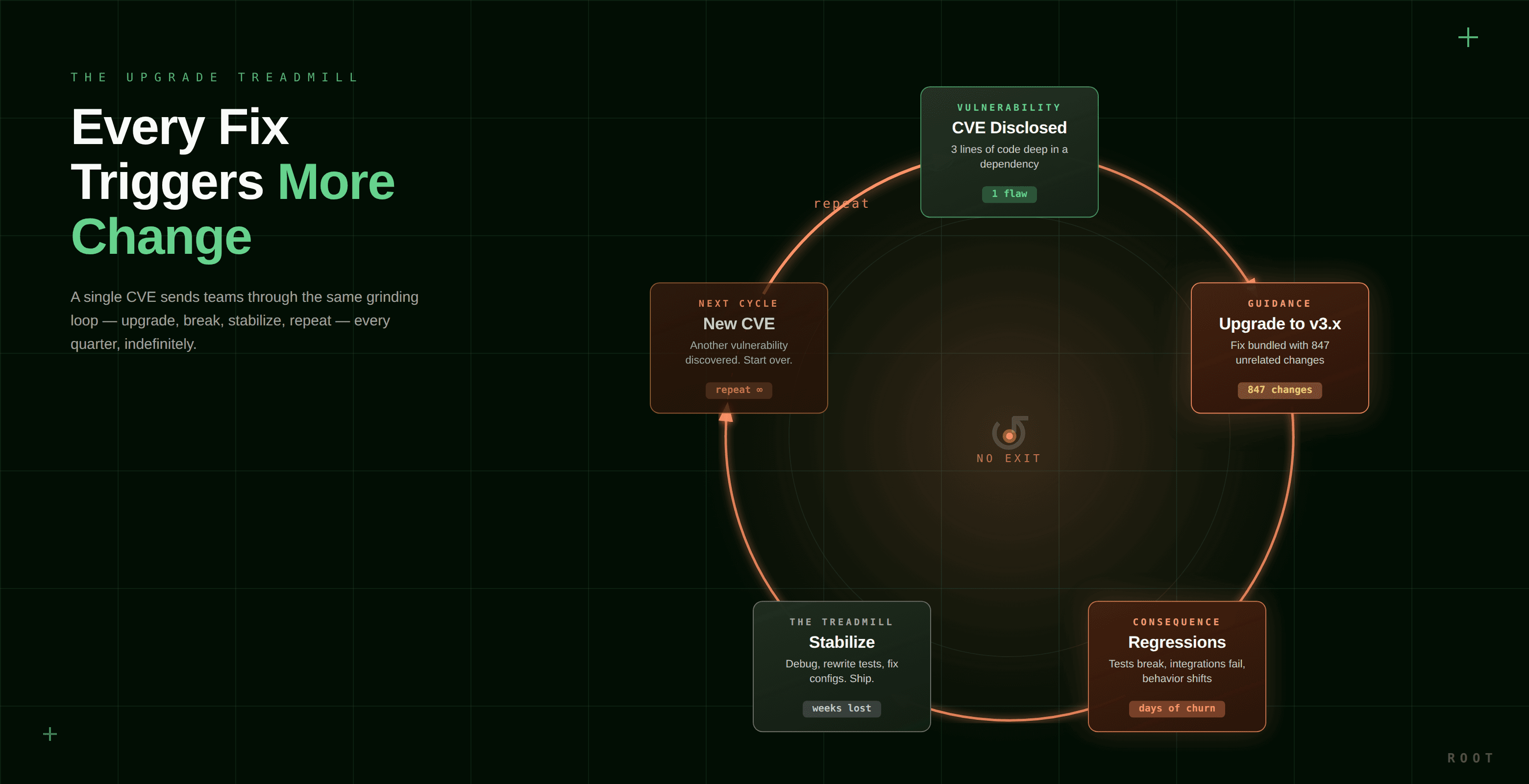
Organizations now find themselves caught in an upgrade treadmill: a continuous cycle of migrations, dependency refreshes, and compatibility fixes triggered by vulnerability disclosures. The intention is to improve security. The practical outcome is often the opposite: more churn, more regressions, and more engineering effort spent managing change rather than eliminating risk.
Understanding why this happens requires looking closely at the relationship between vulnerabilities and the way software is upgraded.
The Structural Problem With Upgrade-Driven Remediation
When a vulnerability is discovered in a dependency, the most common remediation guidance is to upgrade to the version where the vulnerability has been fixed. That guidance seems logical. If the fix is present in a later version, the safest path appears to be moving to that version.
The complication is that version upgrades rarely contain only the security fix.
A new release typically includes a broad collection of changes: new features, refactored code paths, altered behaviors, configuration differences, and updates to additional dependencies. Even minor version increments can alter how software behaves in subtle ways.
This creates a structural mismatch between the problem and the remediation method. The vulnerability itself may be addressed by a relatively small change. The upgrade required to obtain that change may introduce dozens or hundreds of unrelated modifications.
Engineering teams experience the consequences directly. Dependency upgrades frequently trigger failing tests, integration breakage, runtime behavior differences, and compatibility issues across services. These regressions must be investigated and resolved before the system can be safely redeployed.
The irony is that organizations often accept a large amount of operational risk simply to deliver a relatively small security improvement.
The Compounding Effect of Transitive Dependencies
The problem becomes even more pronounced when transitive dependencies are involved.
Most modern software relies heavily on nested dependency chains. A single direct library may introduce dozens of indirect dependencies, each of which may bring its own downstream components. Vulnerabilities frequently appear deep within these layers.
In many cases, the vulnerable code may not even be reachable through the application’s execution paths. Yet remediation guidance still commonly recommends upgrading the entire dependency version that contains the fix.
That upgrade pulls in the entire set of changes introduced since the previous version, not just the security fix. New code paths, altered dependencies, and behavioral differences arrive alongside the patch.
The result is a mismatch between the scope of the risk and the scope of the remediation.
A narrow security flaw can trigger a broad system change. And that system change can introduce new instability, new bugs, or even entirely new vulnerabilities elsewhere in the dependency tree.
Over time, this dynamic creates the upgrade treadmill: a constant effort to move forward through dependency versions in pursuit of security, even as each step introduces new change and new complexity.
Separating Security Fixes From Version Movement
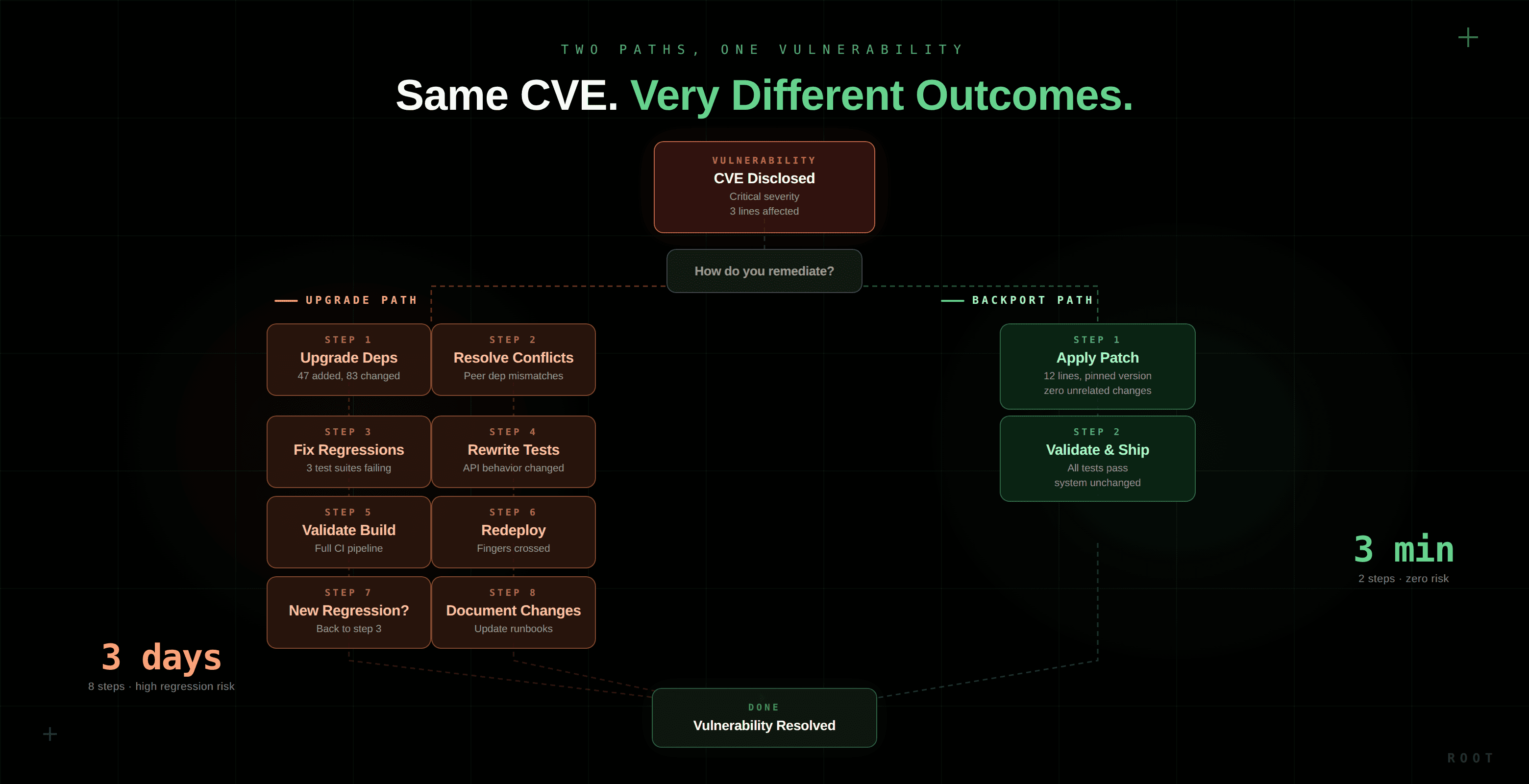
A more effective approach begins by separating two ideas that are often treated as the same thing: applying a security fix and upgrading a dependency version.
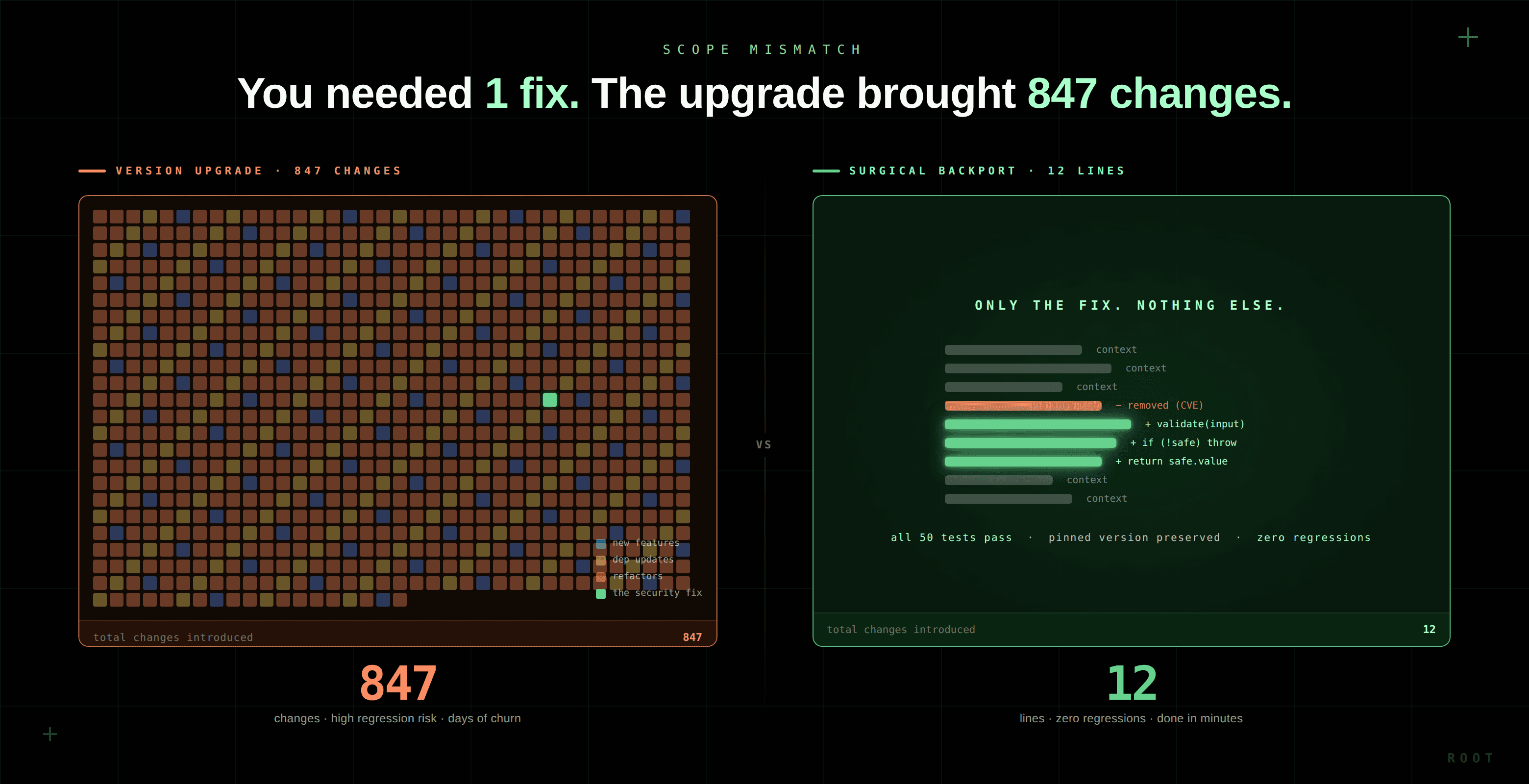
In many cases, the vulnerability fix itself is relatively small. It may involve a few lines of code correcting a validation flaw, tightening a cryptographic check, or fixing a memory handling issue.
There is no inherent reason that change must arrive through a full version upgrade.
Instead, the fix can be applied directly to the version currently deployed in production. This process, commonly referred to as backporting, takes the targeted security patch and applies it to the existing codebase without introducing unrelated changes.
When done carefully, this results in a minimal modification: the vulnerability is removed while the rest of the system remains unchanged.
This distinction matters enormously from an operational perspective. A surgical backport alters only the code necessary to eliminate the vulnerability. A version upgrade alters everything that has changed since the previous release.
By separating security fixes from version movement, organizations can remove vulnerabilities without introducing unnecessary instability.
Stability Through Pinned Versions
This approach naturally leads to the use of pinned dependency versions.
Instead of continuously moving applications to newer dependency versions in response to vulnerabilities, the runtime environment remains stable. Security fixes are applied directly to those versions through carefully scoped backports.
The result is a security process that minimizes transitive change.
Pinned-version patching preserves the existing runtime behavior while addressing vulnerabilities. Engineers review narrowly scoped changes rather than navigating large upgrade diffs. Systems remain stable, even as vulnerabilities are removed.
From a practical standpoint, this model offers several advantages. The amount of code introduced during remediation is dramatically smaller. Regression risk declines. Operational predictability improves.
Security teams gain the ability to remove vulnerabilities without triggering large migrations across dependency trees.
The upgrade treadmill slows down, or disappears entirely.
The Economics of the Upgrade Treadmill
Beyond stability, the economic implications of this shift are significant.
Consider a typical engineering organization running dozens of containerized services. Each service may require periodic upgrades to maintain patch coverage, especially when upstream components reach end-of-life.
Every upgrade cycle involves time spent reviewing dependencies, updating configurations, validating builds, debugging regressions, and redeploying services. Even when these tasks appear small individually, their cumulative effect can be substantial.
A single regression investigation might consume several engineering hours. Multiply that across dozens of services and multiple upgrade cycles per year, and the time cost quickly escalates.
When vulnerability remediation relies primarily on version upgrades, much of the security effort becomes operational overhead.
By contrast, a surgical patching model focuses effort where it matters: applying the fix itself. Engineers review targeted patches and approve artifacts rather than orchestrating full dependency migrations.
The difference in engineering effort can be dramatic. In environments with dozens of services, avoiding upgrade-driven remediation cycles can reclaim thousands of engineering hours annually. That translates directly into reduced operational cost and increased engineering productivity.
Security improves at the same time that operational friction declines.
Meeting Security Requirements Without Disruption
For many organizations, vulnerability remediation is governed by formal service-level expectations. Security teams must demonstrate that vulnerabilities are addressed within a defined timeframe.
Importantly, those requirements rarely mandate running the latest possible version of every dependency. What matters is that the vulnerability itself is eliminated and that the remediation can be verified.
A surgical backporting approach can satisfy these requirements efficiently. By applying the upstream fix directly to the deployed version, patched artifacts can be produced quickly without forcing system migrations.
Automation plays a key role here. Modern remediation platforms can identify upstream patches, apply them to pinned versions, validate the resulting builds, and generate the artifacts necessary for audit and compliance.
Platforms such as Root implement this model by automating the backporting process while preserving full patch provenance, including SBOM updates, VEX statements, signatures, and approval records.
Security fixes arrive rapidly, systems remain stable, and compliance artifacts are generated automatically.
A Different Model for Software Security
The industry’s reliance on version upgrades as the primary remediation mechanism emerged from an earlier stage in the evolution of software systems. In today’s dependency-heavy environments, that approach increasingly imposes costs that outweigh its benefits.
By isolating security fixes from dependency upgrades, organizations can take a more precise approach to vulnerability remediation. Pinned versions provide stability. Surgical backports eliminate vulnerabilities without introducing unrelated change. Automation ensures that patches are delivered quickly and auditable artifacts are preserved.
The result is a security process that is both more predictable and more economical.
Engineering teams spend less time managing migrations and more time building software. Systems remain stable while vulnerabilities are removed. Security improves without the operational turbulence that has become synonymous with dependency upgrades.
In a landscape defined by complex software supply chains, the most effective strategy may not be constant movement forward. It may be something simpler: change only what must be changed, and nothing more.
That philosophy not only reduces the cost of vulnerability remediation. It reshapes how organizations think about the relationship between security, stability, and the economics of modern software systems.
As a side effect, this precision-oriented model also improves resilience against certain classes of software supply chain attacks. Large dependency upgrades introduce wide surfaces for unintended changes or malicious insertions. Surgical patching reduces that surface by limiting modifications to narrowly scoped, auditable security fixes.
In the long run, the most effective security strategy may not be upgrading faster. It may be upgrading less, and fixing vulnerabilities with far greater precision.
If it still won’t preview after pasting this, tell me what editor you’re using (Obsidian, VS Code, Notion, Medium, etc.) and whether you’re pasting into a .md file or a rich text field. Some tools require a specific “Markdown mode,” and a couple treat triple-dash separators differently.
Continue Reading









