Blog
Root Now Supports Go
Root now publishes backported Go modules for CVEs that don't have fixes in the version line you're using.

Beatriz Datangel Rodgers
Head of Product Marketing
Published :
May 14, 2026

In Python, a CVE fix is pip install. In npm, npm update. In Go, the harder problem is often that the fix doesn't exist on the version line your application is pinned to. The upstream maintainer published the patch on main or on a major version your codebase isn't on yet. You're left choosing between an upgrade that drags in unrelated changes, or accepting a known vulnerability.
Root closes that gap. Go is now live on Root.
Root publishes backported Go modules for CVEs that don't have fixes in the version line you're using. The Root Patcher CLI analyzes your go.mod, finds the modules with Root patches available, and adds replace directives pointing at the backported versions. Your import paths don't move. Your application code never changes. Only go.mod picks up the redirects, and go mod tidy resolves the rest.
This is the fourth ecosystem in the Root Library Catalog, alongside Python, JavaScript, and Java.
How it works
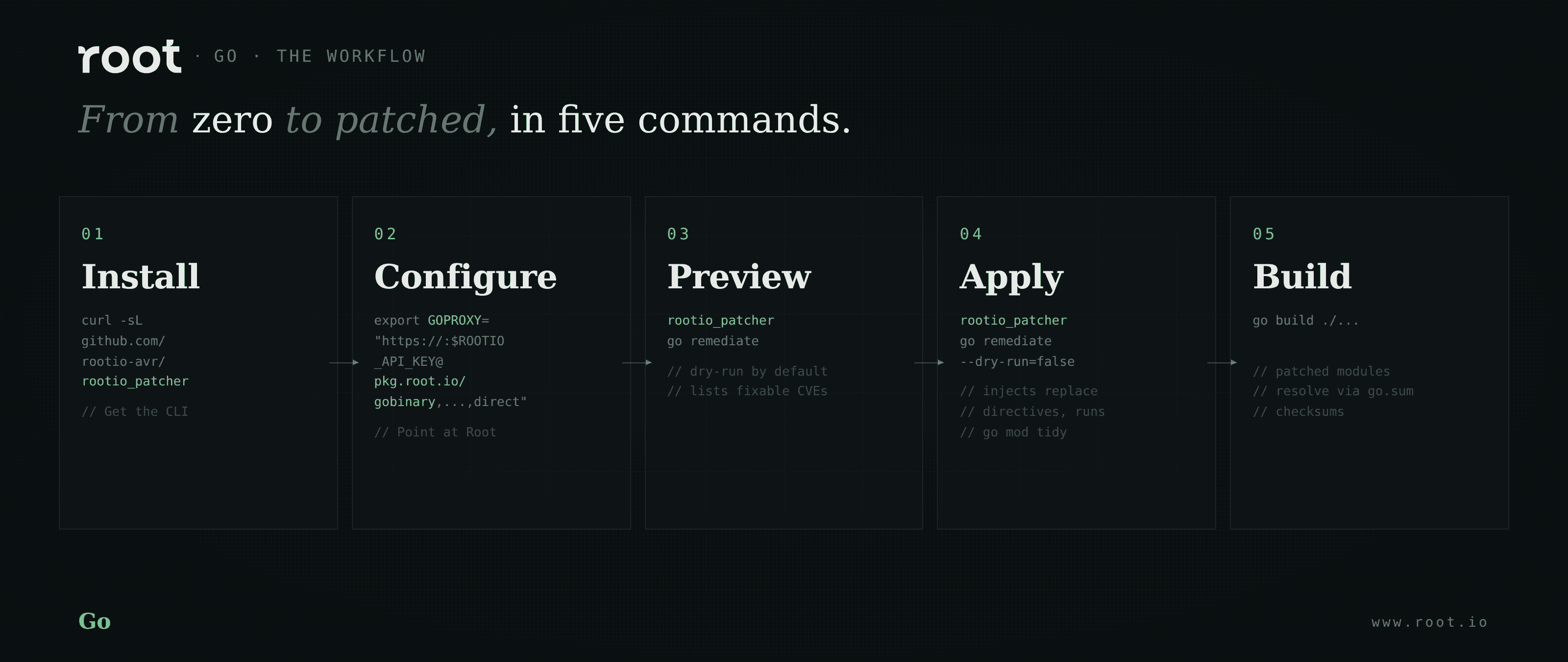
Install the Root Patcher CLI, set your API key, and configure GOPROXY:
Preview which Root patches are available for your project:
The patcher runs in dry-run mode by default and reports which modules have Root-patched versions and which CVEs each one fixes. To apply:
The patcher adds replace directives to go.mod, runs go mod tidy to fetch the patched modules, and writes the correct checksums into go.sum. A patched go.mod looks like this:
Patched versions carry a -rootio.N suffix, so it's obvious at a glance which modules Root is serving and which release they were backported from. Commit go.mod and go.sum together. From there, builds in CI use the checksums in go.sum for verification, no extra environment variables required beyond GOPROXY.
What's covered
The Library Catalog covers the Go module ecosystem broadly: the golang.org/x/* packages, common HTTP and crypto libraries, gRPC, Kubernetes client libraries, observability collectors, and the modules embedded in widely-used infrastructure tools.
A few constraints worth knowing up front:
Pinned semver only. Modules using pseudo-versions (v0.0.0-20230101...) are skipped. Upgrade to a pinned release before running the patcher.
Standard library is not in scope. Go's stdlib is part of the toolchain itself and can't be redirected via replace directives. For stdlib CVEs, the recommended path is to keep your Go version current. The Go team's backwards-compatibility guarantees make this comparatively cheap.
Multi-module repos are supported. Run the patcher per module: rootio_patcher go remediate --go-mod=./services/api/go.mod --dry-run=false.
When a CVE lands on a module Root is watching, the agentic patching pipeline picks it up and starts generating a backport. Turnaround is typically measured in days.
Every patched module ships with an updated SBOM (CycloneDX), a VEX statement, and a provenance attestation.
Try it
Full product access is free until May 31, 2026. Install the patcher, configure GOPROXY, and run rootio_patcher go remediate against your repo to see which CVEs Root can clean up.
Full configuration docs: docs.root.io/rlc/go
Related reading
Continue Reading









