Blog
See Exactly How Root Fixes Every CVE
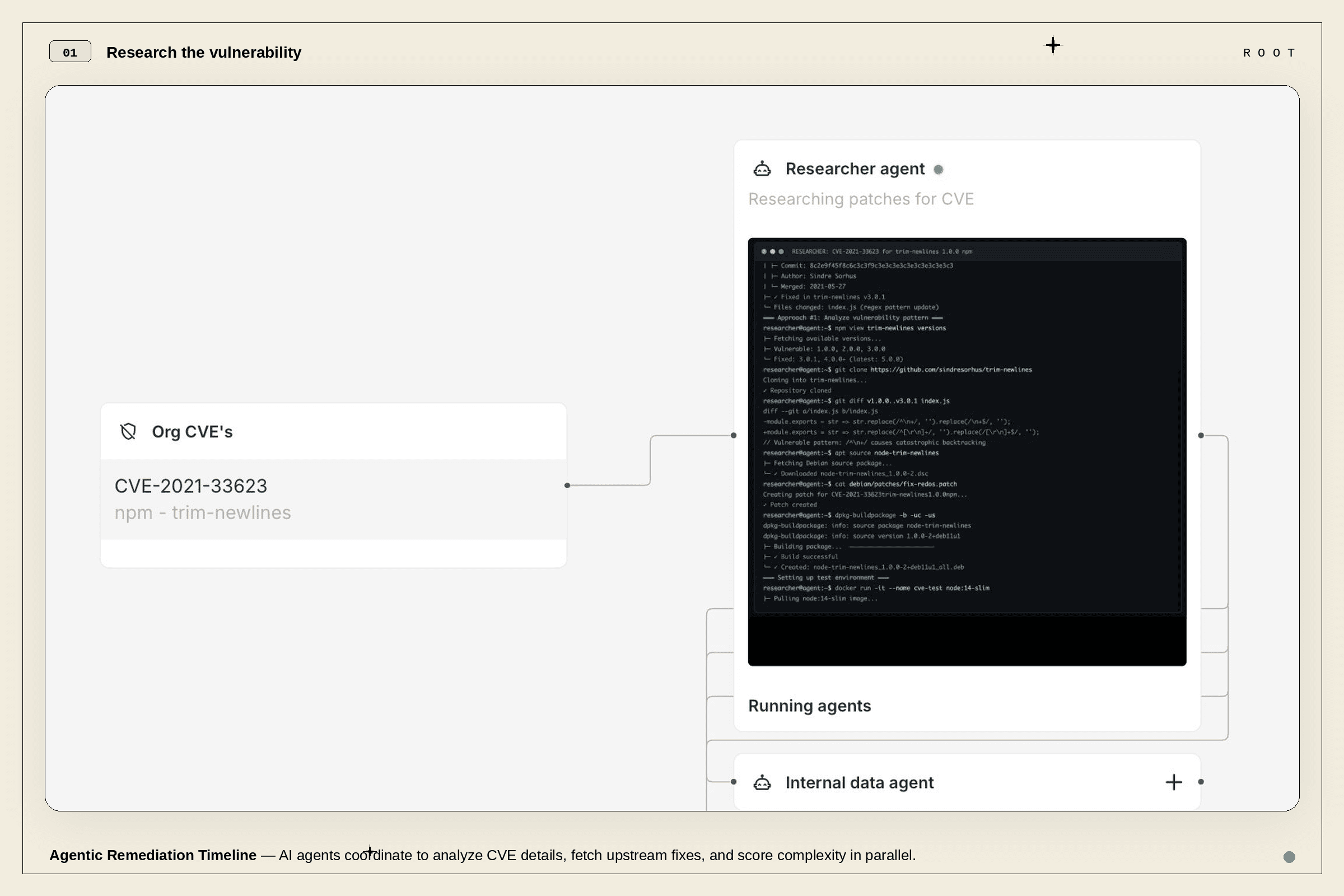
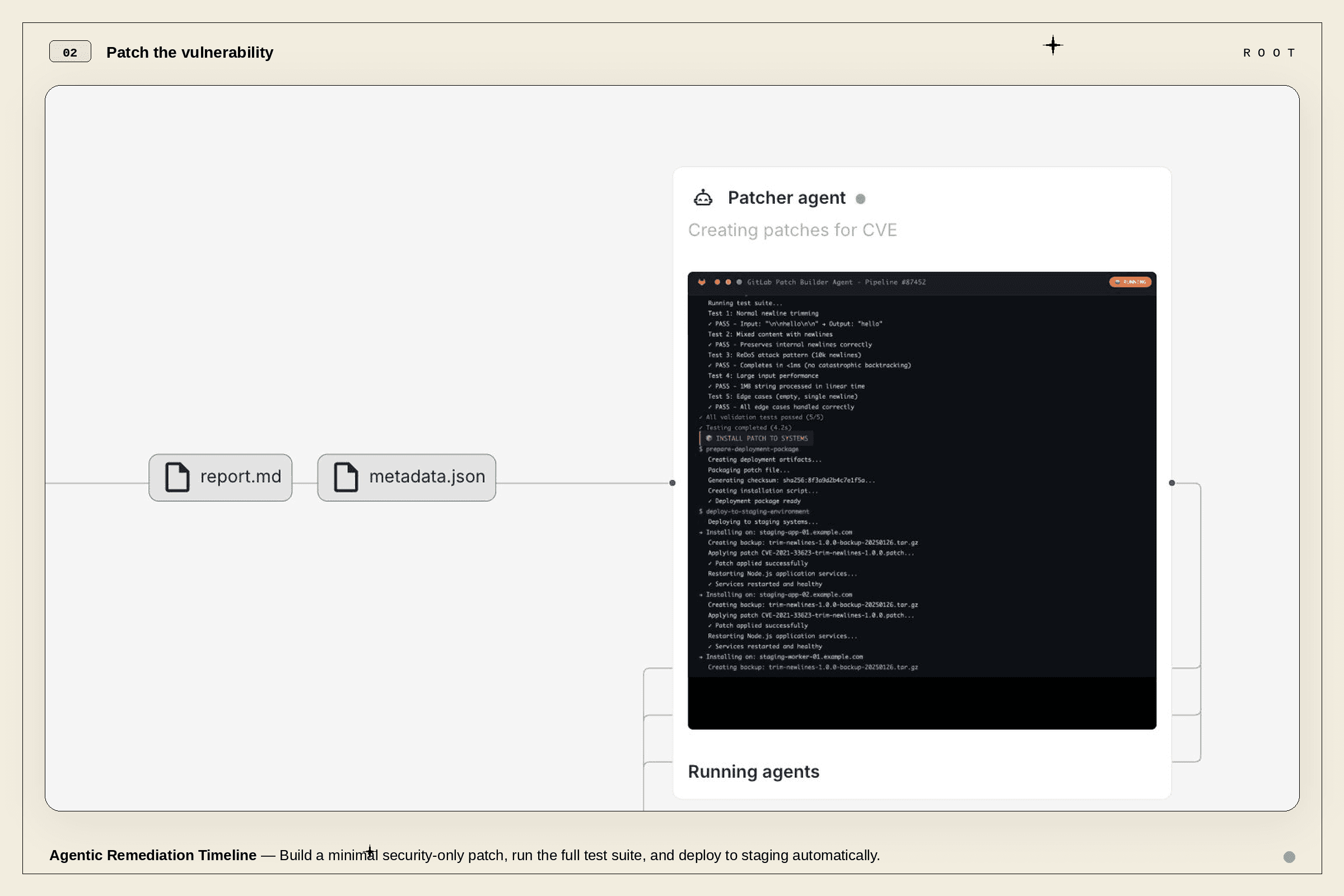
Introducing Root's Agentic Remediation Timeline: a step-by-step view of every action Root's AI took to research, patch, and validate your vulnerability fixes.

Mickey Gordon
CPO, Co-Founder
Published :
Feb 25, 2026
You wouldn't trust a mechanic who said "it's fixed" and handed you the keys. You'd want to know what they found, what they replaced, and how they tested it.
So why do security teams accept that from their remediation tools?
Most automated patching works like a black box. A vulnerability goes in, a fix comes out, and you're supposed to trust that everything in between was done right. Starting today, every CVE remediated by Root includes a full Agentic Remediation Timeline: a transparent record of every decision our AI made to fix your vulnerability. No black boxes. No "just trust us." Every action, every validation, every result, visible directly in your image report, package report, or vulnerabilities page.
Why This Is Different
Most patching tools query a static database, match a CVE to a known fix, and ship it. Root's AI agents carry deep, in-house knowledge of how to patch, accumulated across thousands of remediation cycles across 14+ package ecosystems. Root doesn't just know what to fix. It knows how to fix it for your specific package version, ecosystem, and environment. And now you can see that entire reasoning process unfold, step by step.
What You'll See
Open any remediated CVE and you'll find a timeline view that walks through four phases: Research, Patch, Validate, and Deliver. It looks like a CI/CD pipeline, because that's essentially what it is. Except instead of building your app, it's fixing your vulnerabilities. The underlying cycle: plan → act → build → test → repeat until succeeded.
Research. Root runs a coordinated research process across multiple sources simultaneously: internal knowledge matches (deploying known fixes in ~60 seconds), NVD and distribution tracker lookups, upstream fix analysis, exploitability assessment (is a PoC publicly available?), and complexity scoring. The phase ends with a clear outcome and the evidence behind it.
Patch. Root generates a minimal, security-only patch targeting the vulnerability and nothing else. You'll see the source diff, ecosystem-aware formatting across 14+ package managers, and full build status, including retries if the build fails.
Validate. This is where Root earns your trust. Three validators run in parallel on every patch:
Patch Security Analysis scans for dangerous patterns like command injection, buffer overflows, and unsafe deserialization, then assigns a security score. Anything below threshold stops the pipeline.
Proof-of-Concept Verification runs known exploits against both unpatched and patched versions. Concrete proof the vulnerability is mitigated.
Functional Testing compares test suite results against the pre-patch baseline. If the fix broke something, this catches it.
All validators must pass. No exceptions.
Deliver. Every patch is reviewed by Root's Security Analyst, the key agent responsible for the final quality gate. The timeline shows the final status and links to every artifact.
When the AI Calls for Human Review

Root's AI knows what it doesn't know. When the Security Analyst flags a patch for deeper human inspection due to unusual complexity, edge-case behavior, or low-confidence scoring, the timeline makes it explicit: why the AI escalated, what concerned it, and what a reviewer should focus on.
Every stage generates structured data (scores, test outcomes, coverage metrics) that cascades forward. By the time a patch reaches a human reviewer, they get a complete recap of every decision and result. No digging through code diffs. No re-running tests.
This isn't a failure mode. It's a trust signal.
Why This Matters
For security teams: Every remediation decision is documented automatically. When leadership asks "how did we fix this?" the answer is one click away.
For compliance: SOC 2, FedRAMP, PCI DSS all want audit evidence. The Agentic Remediation Timeline generates it as a byproduct of doing the work. No retroactive documentation.
For engineering leaders: The triple validation for every fix (patch security analysis, exploit verification, and functional testing) is all visible, all auditable.
The Numbers

For known fixes, Root's fast-path completes in ~60 seconds. For new research, the full pipeline runs in 30–45 minutes. The industry average? 7–17 days. That's up to a 340× improvement, deployed at the application level with no package upgrades and no dependency hell.
See It in Action
The Agentic Remediation Timeline is available now for all Root customers. Open any remediated CVE in your image report, package report, or vulnerabilities page.
Not a Root customer yet? Book a demo and we'll walk you through a live remediation, from CVE disclosure to validated patch.
Continue Reading









