Blog
Trivy, LiteLLM, and axios Were Compromised. Root Already Has the Fix.
Free trial, full product access. Secured versions of dozens of packages hit in Q1 2026, deployed in minutes.

Root team
The Root team
Published :
Mar 31, 2026
Trusted updates compromised 100,000+ companies in Q1 2026. Pin your dependencies, patch in place, and remove the attack path entirely.
In Q1 2026, dozens of packages across Docker Hub, PyPI, and npm were compromised in a series of coordinated supply chain attacks. Security tools, AI infrastructure, and one of the most depended-on libraries in JavaScript, all hit within days of each other.
Root has already produced secured versions for all ten.
The teams cleaning up these incidents need more than another scanner. And the teams that weren't hit need a way to make sure luck isn't part of their security model. That is why we are launching a free, self-service trial of Root with full product access.
What follows is what happened, why existing approaches failed, and how to fix the exposure now.
Industrialized attacks meet trusted distribution
Two forces converged this quarter.
AI has made it trivial to generate malicious packages at scale. Attackers can produce, mutate, and redeploy packages faster than defenders can analyze them. At the same time, open source registries remain the most efficient distribution system in software. Fast, global, and implicitly trusted.
The result: attackers published 454,648 malicious packages across Maven Central, PyPI, npm, and NuGet in the past year, targeting ecosystems responsible for 9.8 trillion downloads.
When distribution is instant, security has to be as well.
The five-day campaign that changed everything
In March, the TeamPCP campaign made this shift impossible to ignore.
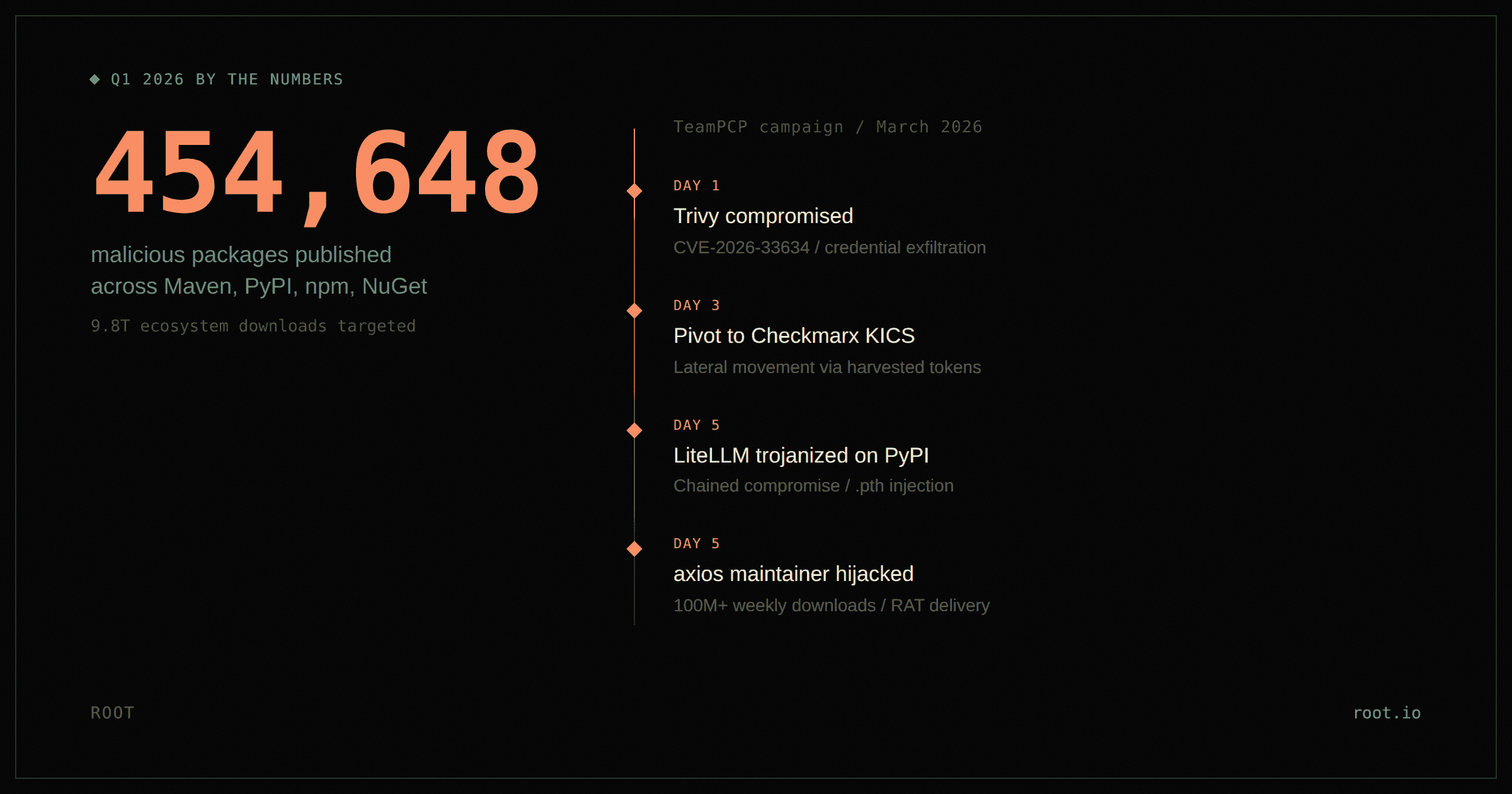
Within five days, Trivy (CVE-2026-33634), a widely used vulnerability scanner, was compromised. Attackers pivoted into Checkmarx KICS, then into LiteLLM on PyPI. In parallel, the axios compromise on March 31 hit a package with over 100 million weekly downloads through a maintainer account hijack.
These attacks didn't exploit vulnerable code. They poisoned trusted artifacts. The vulnerability wasn't in the code. It was in the software being trusted. Tools designed to detect vulnerabilities were themselves exfiltrating credentials. Cloud tokens, Kubernetes secrets, database access, all harvested and sent to attacker-controlled infrastructure. From the perspective of a scanner analyzing source code, nothing appeared wrong.
One compromise was no longer the end of an attack. It was the beginning of the next one. Credential theft became lateral movement. Lateral movement became distribution. Distribution became the next breach.
This isn’t a wave. It is an operating condition.
Two kinds of teams are reading this
Some teams are already cleaning up the damage. Their pipelines pulled in compromised dependencies. Their security tools were part of the attack chain. Their CISO is asking how this happened and how it won’t happen again.
Other teams weren’t hit this time. But if they still rely on auto-updated dependencies, they are exposed to the exact same path. They aren’t safer. They are earlier.
The trap
Teams are now caught between two bad options.
Option 1: Keep auto-updating. You stay current, but you are trusting the same update path attackers are using to distribute malicious code.
Option 2: Pin your dependencies. You reduce that attack path, but now every CVE fix requires upgrades, rebuilds, and regression testing. Remediation slows to a crawl.
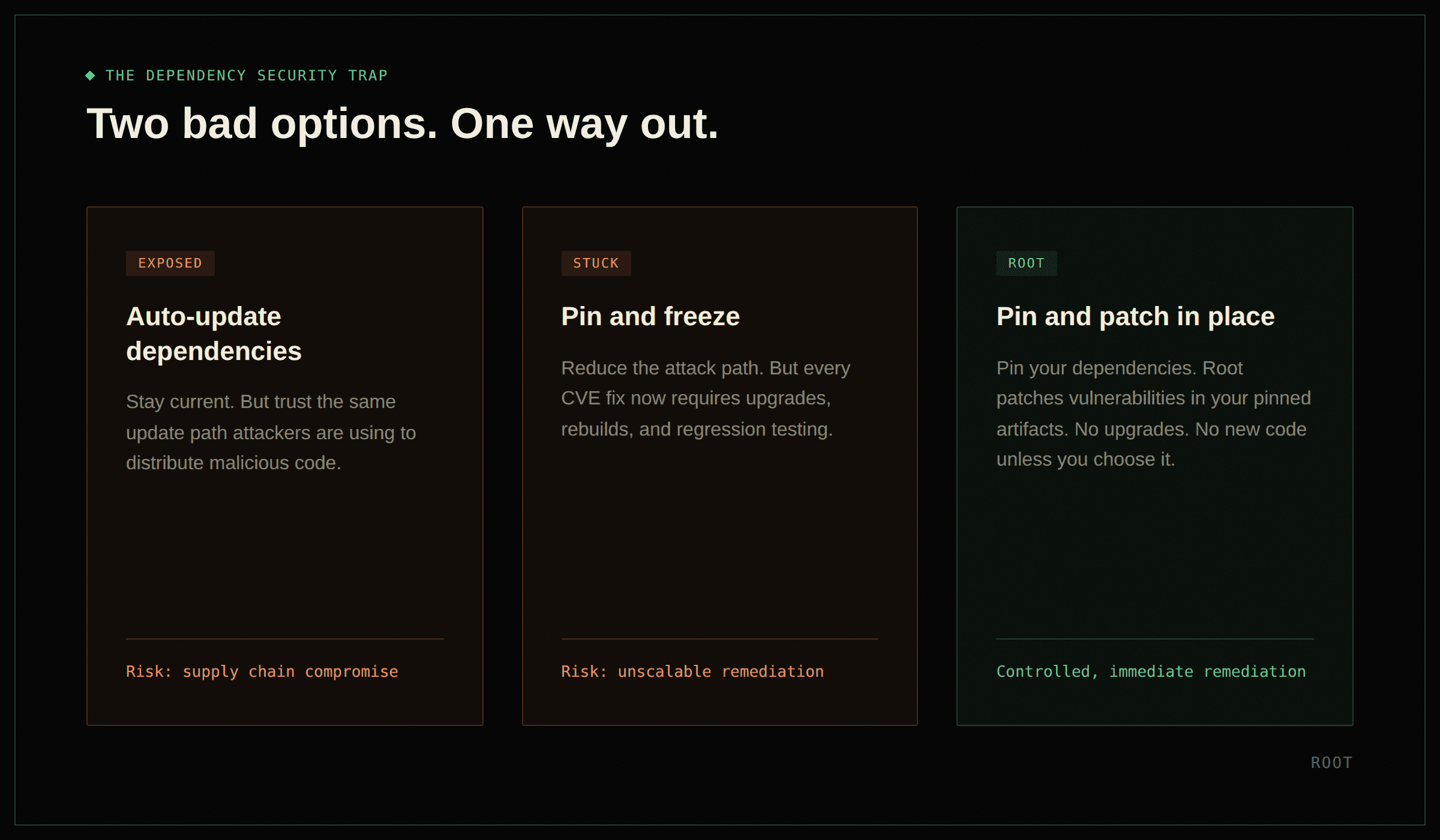
Either way, these packages are in your dependency tree. And the model that put them there is broken.
How Root breaks the trap
Root removes the tradeoff entirely.
You pin your dependencies, so no unexpected upstream changes introduce malicious code. Root then patches those pinned artifacts in place, so vulnerabilities are fixed without upgrades. No new code enters your environment unless you choose it.
No auto-updates. No forced rebuilds. No waiting on upstream fixes. Just controlled, immediate remediation.
This is the model we have been building toward. We have shown how remediation can happen without rebuilding images and how security can be embedded directly into developer workflows. Q1 proved why it matters.
Try it now
To help teams respond to what is already happening, Root is offering a free, self-service trial covering container images and application libraries for 2 months (ending May 31, 2026). Full product access, automatic provisioning, no strings.
The free trial includes full product access: UI, API, and package registry for both container images and application libraries.
Root has already produced secured versions for every package compromised in Q1's supply chain campaigns:
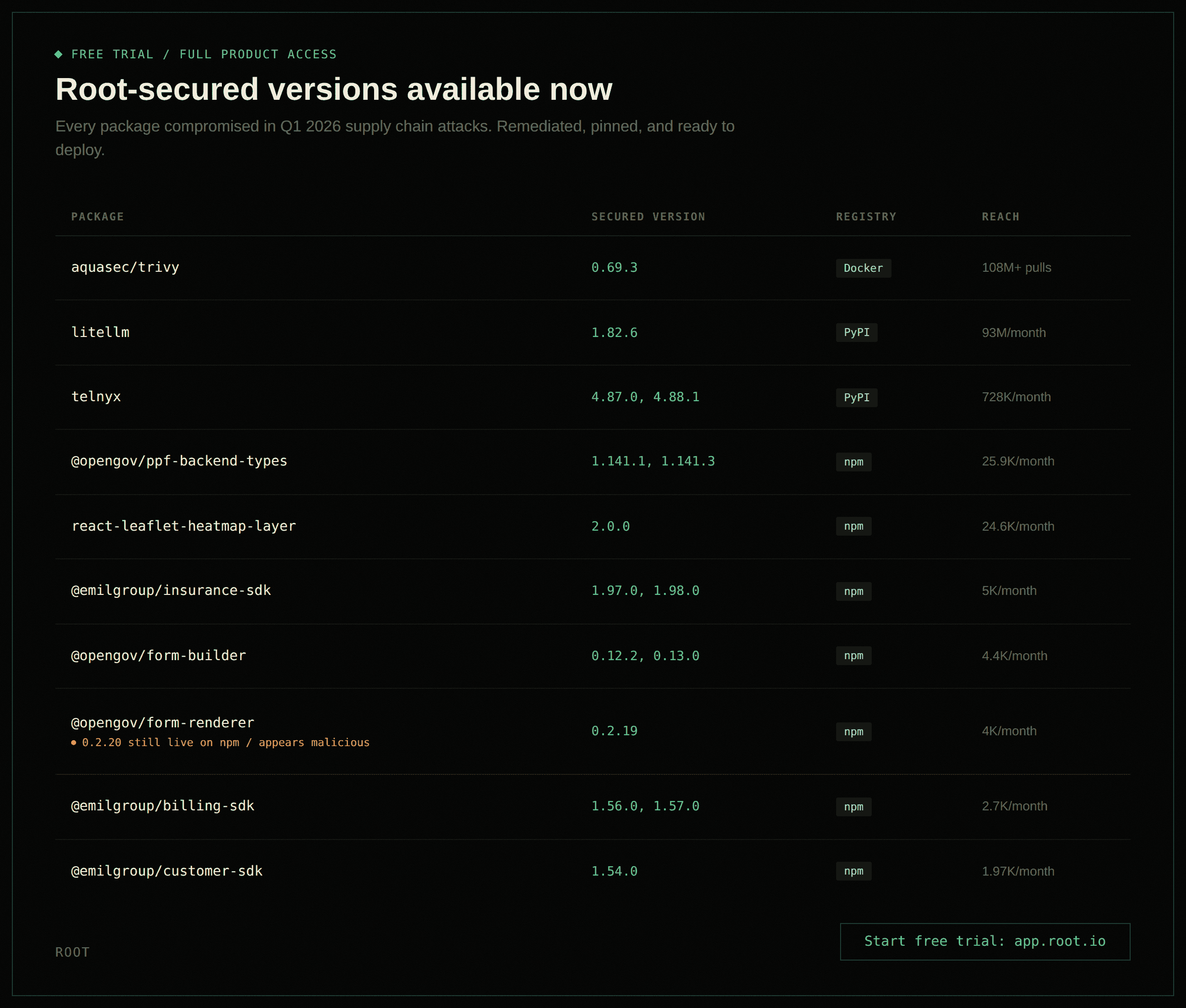
Root replaces these compromised artifacts with known-good, remediated versions in minutes, while keeping your dependencies pinned and your attack surface controlled.
This isn't a demo environment. It is the full product, applied to the exact failure mode Q1 exposed.
The takeaway
Q1 2026 didn’t introduce supply chain attacks. It normalized them.
The registry layer is no longer a reliable source of truth. It is an active source of risk. If you still rely on updating dependencies to stay secure, you are relying on the same mechanism attackers are exploiting.
Pin your dependencies. Patch them in place. Remove the attack path entirely.
Continue Reading









